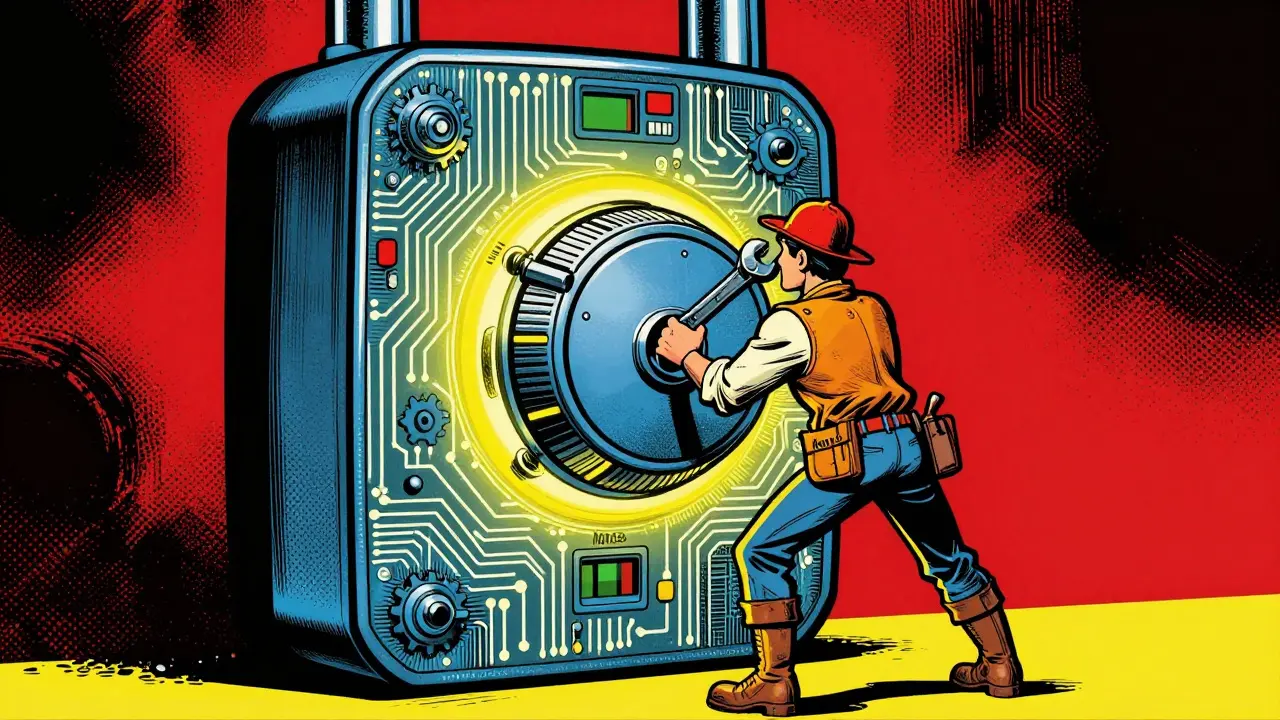
Imagine you are trying to guess a combination lock. You don't know the code, so you just try numbers one by one until it clicks open. That is exactly how Nonce, short for "number used once," works in blockchain mining. It is not magic. It is brute force. In the world of Proof of Work (PoW), the nonce is the variable that miners change over and over again to solve a cryptographic puzzle. Without it, blockchains like Bitcoin would have no way to secure transactions or prevent fraud.
You might wonder why we need such a simple concept to protect billions of dollars. The answer lies in how difficult it is to find the right number, yet how easy it is to check if it is correct. This asymmetry is the backbone of decentralized security. Let’s break down what a nonce actually does, how miners use it, and why it remains critical despite newer technologies emerging.
What Is a Nonce in Blockchain?
A nonce is an arbitrary value included in a block header. Its only job is to make the resulting hash meet specific criteria set by the network. In Bitcoin, this means finding a hash with enough leading zeros. Think of it as a target score in a game. The lower the score (more zeros), the harder it is to achieve.
When a miner collects transactions into a block, they create a header containing several pieces of data:
- The previous block’s hash
- A timestamp
- The Merkle root (a summary of all transactions)
- The difficulty target
- The nonce
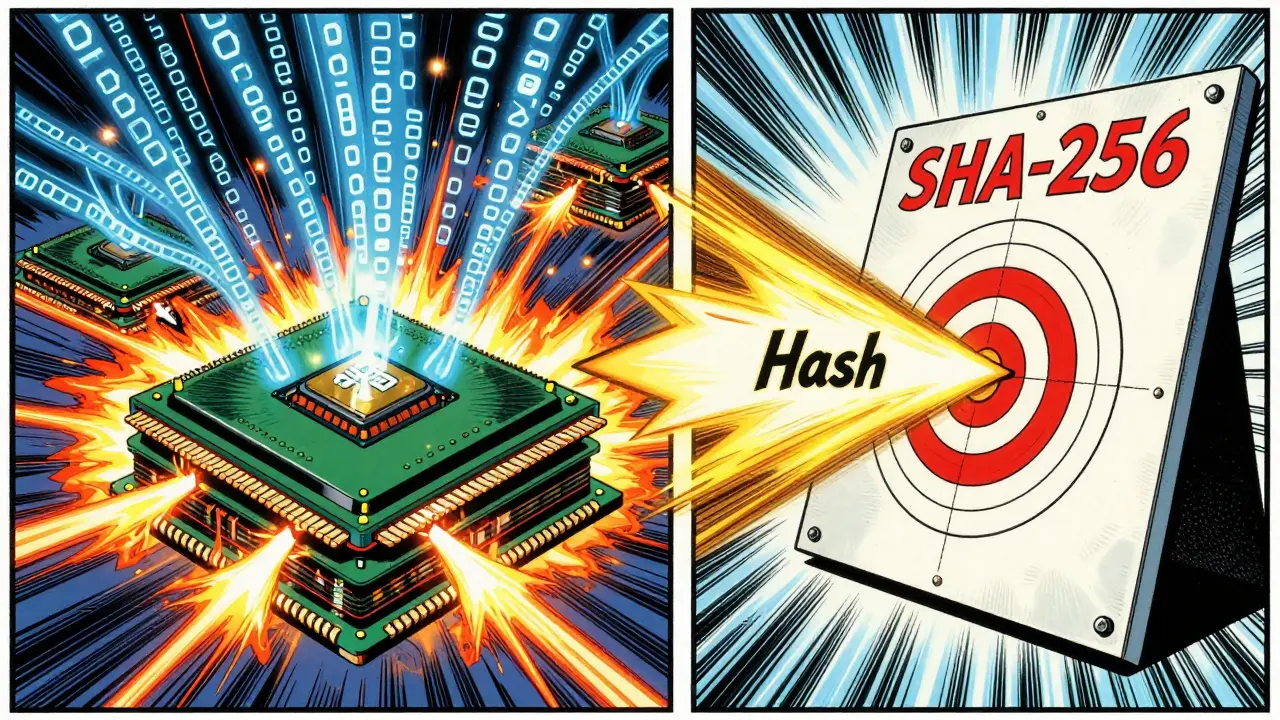
Miners run this entire header through the SHA-256 hashing algorithm. If the output doesn’t match the difficulty requirement, they change the nonce and try again. They start at zero, then one, then two, continuing until they find the "golden nonce." Once found, the block is broadcast to the network, and everyone can instantly verify it is valid.
This process ensures that creating a block requires significant computational effort. It also makes altering past blocks nearly impossible because changing even one transaction would require recalculating the nonce for that block and every block after it.
How Miners Find the Golden Nonce
Finding a valid nonce is a race against time and other miners. Since hash functions cannot be reversed, there is no shortcut. Miners must guess. This is where specialized hardware comes in. Early Bitcoin miners used regular CPUs, but today, most rely on ASICs (Application-Specific Integrated Circuits). These chips are designed solely to perform SHA-256 calculations at incredible speeds.
Here is the step-by-step process a miner follows:
- Gather unconfirmed transactions from the mempool.
- Construct a candidate block with a header.
- Set the nonce to zero.
- Hash the header using SHA-256.
- Check if the hash meets the current difficulty target.
- If not, increment the nonce by one and repeat.
This loop runs millions of times per second. When a miner finds a valid hash, they announce it. Other nodes verify the solution quickly because checking a hash is computationally cheap compared to finding it. The successful miner receives a block reward plus transaction fees. This incentive structure keeps the network secure and decentralized.
The difficulty of finding a nonce adjusts automatically every 2,016 blocks, which takes about two weeks. If miners add more power to the network, the difficulty increases to keep block times around ten minutes. This adjustment ensures stability regardless of how many people are mining.
Why Proof of Work Needs Nonces
Proof of Work relies on nonces to create economic security. The energy and hardware required to find nonces act as a barrier to entry. To attack the network, a malicious actor would need to control more than 50% of the total hashing power. This is prohibitively expensive for large networks like Bitcoin.
Nonces also prevent Sybil attacks, where someone creates multiple fake identities to manipulate the system. In PoW, identity doesn’t matter; only computational power does. This promotes fairness and decentralization. Anyone with electricity and hardware can participate, regardless of who they are.
Critics often point out the high energy consumption of nonce-based mining. While true, this energy expenditure serves a purpose. It translates directly into security. The cost of attacking the network far exceeds any potential gain. Alternative consensus mechanisms like Proof of Stake (PoS) eliminate nonces entirely. Instead, validators stake coins to secure the network. However, PoS lacks the same level of cryptographic certainty provided by PoW. For applications prioritizing maximum security, nonces remain unmatched.
Nonce vs. Other Consensus Mechanisms
To understand the unique role of nonces, compare them to other methods. Below is a comparison table highlighting key differences between Proof of Work and Proof of Stake.
| Feature | Proof of Work (PoW) | Proof of Stake (PoS) |
|---|---|---|
| Core Component | Nonce | Staked Coins |
| Security Basis | Computational Power | Economic Stake |
| Energy Usage | High | Low |
| Hardware Required | ASICs/GPUs | Standard Servers |
| Finality | Probabilistic | Deterministic (often) |
| Example Networks | Bitcoin, Litecoin | Ethereum, Cardano |
Ethereum famously switched from PoW to PoS in September 2022 during "The Merge." This move reduced its energy usage by over 99%. However, Bitcoin continues to use PoW because its primary goal is secure digital gold storage. The trade-off is clear: PoW offers superior immutability at the cost of efficiency. PoS offers speed and low costs but relies on different security assumptions.

Practical Implications for Miners
If you are considering mining, understanding nonces is crucial. You cannot simply pick a random number and hope for the best. You need reliable software that automates the trial-and-error process. Popular mining software includes CGMiner and BFGMiner, which handle nonce iteration efficiently.
Profitability depends on several factors:
- Electricity costs: Cheap power is essential.
- Hardware efficiency: Newer ASICs generate more hashes per watt.
- Network difficulty: Higher difficulty means lower rewards per hash.
- Block size limits: Bitcoin blocks max out at 1MB (or 4MB with SegWit), limiting transaction volume per block.
As competition grows, individual miners often join pools to share rewards. Pool mining smooths out income volatility by distributing payouts based on contributed hashing power. Even in a pool, your hardware still searches for nonces independently. The first miner to find a valid nonce claims the reward, which is then shared according to pool agreements.
For beginners, the learning curve involves grasping cryptographic basics. You don’t need to understand every mathematical detail, but knowing how SHA-256 works helps demystify the process. Remember, mining is rigorous work. It requires dedication, investment, and patience. There are no quick riches here.
Future of Nonce-Based Security
Despite criticism, nonce-based Proof of Work shows no signs of disappearing. Bitcoin’s dominance in market cap and trust stems largely from its battle-tested security model. Innovations like the Lightning Network operate atop this base layer, enhancing scalability without compromising security.
Future developments may focus on making mining hardware more energy-efficient. Researchers are exploring ways to reduce power consumption while maintaining hash rates. Additionally, some projects experiment with hybrid consensus models, combining PoW and PoS elements. However, pure PoW remains the gold standard for networks requiring absolute tamper-proofing.
In conclusion, the nonce is far more than a random number. It is the engine driving blockchain security. By forcing miners to expend real-world resources, it creates an economic deterrent against attacks. As long as value needs secure, decentralized storage, nonces will continue to play a vital role.
Can I reuse a nonce in Bitcoin mining?
No, each nonce must be unique for a specific block attempt. Reusing a nonce would result in the same hash, which likely won’t meet the difficulty target. Miners increment nonces sequentially to ensure uniqueness.
What happens if two miners find a valid nonce at the same time?
This causes a temporary fork in the blockchain. Nodes accept both blocks initially. Eventually, one chain becomes longer due to subsequent blocks being added. Miners switch to the longest chain, and the orphaned block’s transactions return to the mempool.
Why does Bitcoin use SHA-256 instead of other algorithms?
SHA-256 was chosen for its robustness, speed, and resistance to collisions. It provides a good balance between computational difficulty and verification ease. Other algorithms exist, but SHA-256 has proven effective over decades.
Is mining profitable without ASICs?
Generally no for Bitcoin. ASICs dominate the market due to their efficiency. CPU or GPU mining is only viable for smaller altcoins with lower difficulty levels. For Bitcoin, ASICs are necessary to compete.
How does the nonce relate to block difficulty?
Higher difficulty requires more leading zeros in the hash, meaning fewer valid nonces exist. Miners must test more values before finding a match. Difficulty adjusts periodically to maintain consistent block times.