Blockchain: Guides, Tools & Trends for Every Skill Level
When working with Blockchain, a distributed ledger technology that records transactions across a network of computers. Also known as distributed ledger, it powers most of today’s crypto assets and new Web3 applications.
One of the fastest‑growing sub‑fields is Modular blockchain, a design that separates data availability, consensus and execution into distinct layers. This split lets developers swap out consensus engines without rebuilding the whole network, which in turn boosts scalability and reduces upgrade risk. For example, Celestia’s data‑availability layer lets rollup projects focus on smart‑contract logic while relying on a secure, shared availability service. Blockchain therefore encompasses both monolithic chains like Bitcoin and these modular alternatives, each with its own trade‑offs for speed, security and developer flexibility. The modular approach directly influences scalability, because it isolates heavy data traffic from consensus processing, allowing each layer to optimize its own parameters.
Security, Identity and Governance in Modern Blockchains
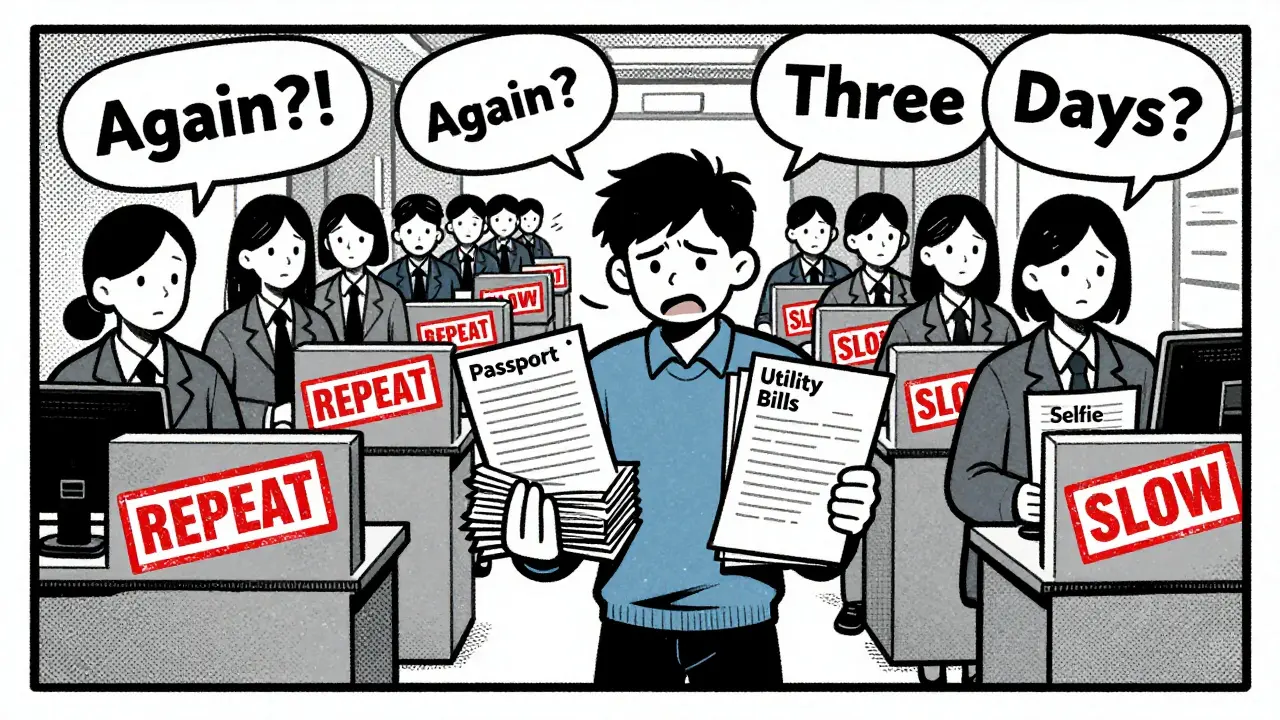
Another cornerstone of today’s ecosystems is Proof of Stake, a consensus mechanism where validators lock up tokens to secure the network and earn rewards. PoS replaces energy‑intensive mining with staking, but it also introduces new risks like slashing – the automatic penalty for misbehaving validators. Effective slashing protection tools, such as CubeSigner, let operators monitor performance, auto‑recover keys and avoid costly penalties. Proof of Stake therefore requires robust validator management and reliable monitoring to keep the network safe.
Beyond raw security, blockchain is reshaping how we prove who we are. Self‑sovereign identity, a user‑controlled digital identity model that stores credentials on a decentralized ledger puts personal data back in the hands of its owner. Instead of relying on centralized providers, users can present cryptographic proofs to services, reducing data breaches and giving them granular control over sharing. This identity model fuels new use cases like decentralized voting, where blockchain voting, a system that records ballots on an immutable ledger ensures transparency, tamper‑resistance, and auditability. The combination of PoS security, SSI privacy and voting transparency builds a more trustworthy ecosystem for everything from corporate governance to national elections.
All of these topics intersect across the articles below. You’ll find deep dives into Celestia’s modular architecture, step‑by‑step guides for slashing protection, practical overviews of SSI implementation, and clear explanations of how forks and voting systems shape blockchain governance. Whether you’re a developer building the next rollup, a validator protecting assets, or a citizen curious about secure digital voting, the collection offers concrete advice you can act on right now. Dive in to see how each piece fits into the broader puzzle of today’s blockchain landscape.